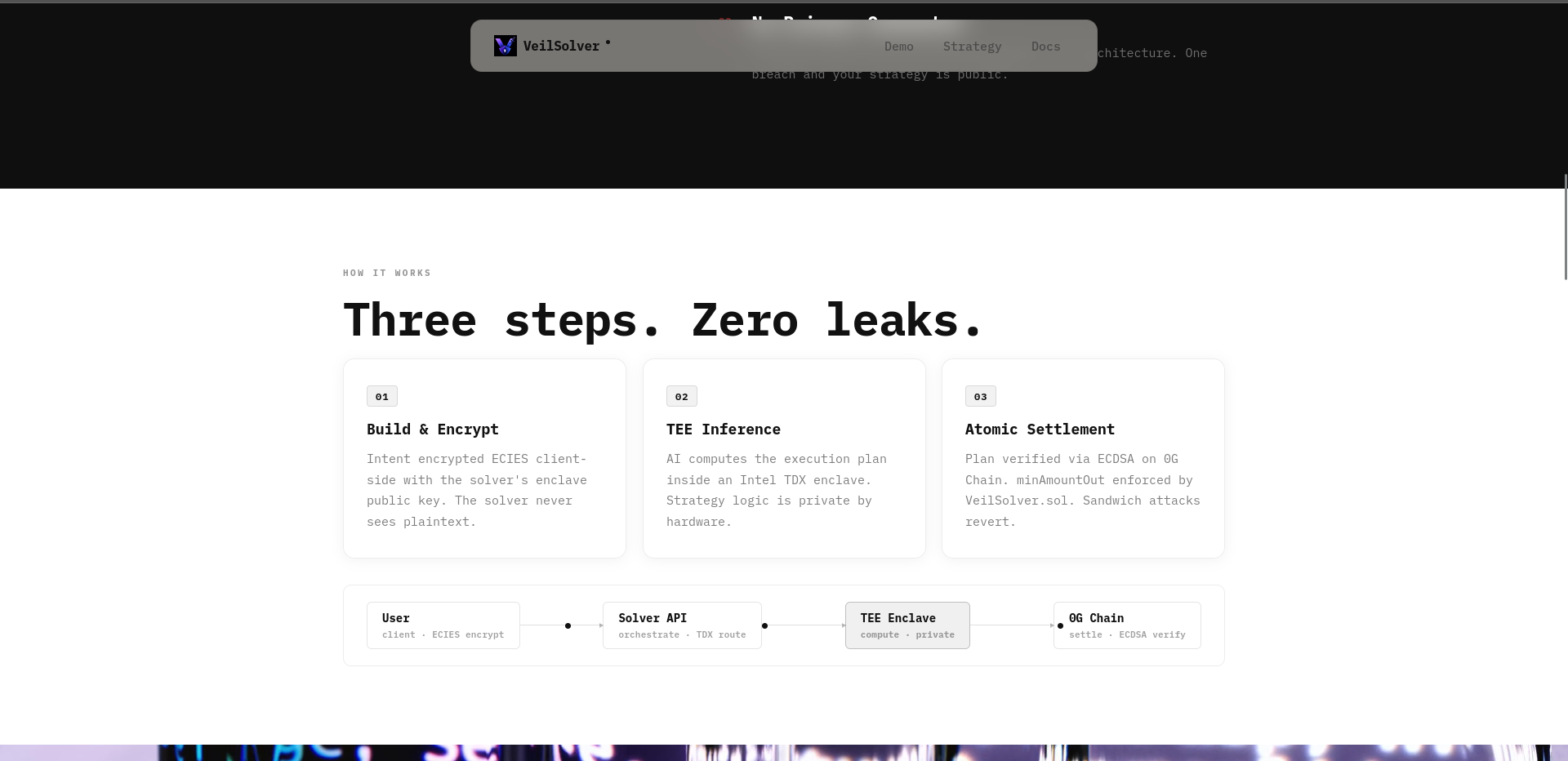
Private intent solver on 0G. Encrypted trades execute inside Intel TDX enclave — operator blind, MEV-proof. ECDSA-signed plans settle atomically on 0G Chain. Your strategy never leaks.

DeFi loses over $1B annually to MEV. The industry's response has been to protect
transactions at the mempool layer. That's the wrong fix. The real leak happens
earlier — in the AI strategy that decided what to trade, when, and how much. Once
that signal is visible, MEV bots don't need to front-run your transaction. They
already know your move.
VeilSolver is a private intent solver: a system where a user's trading strategy is
computed inside a Trusted Execution Environment, cryptographically signed, and
settled atomically onchain — without the strategy ever being readable by anyone,
including the operator.
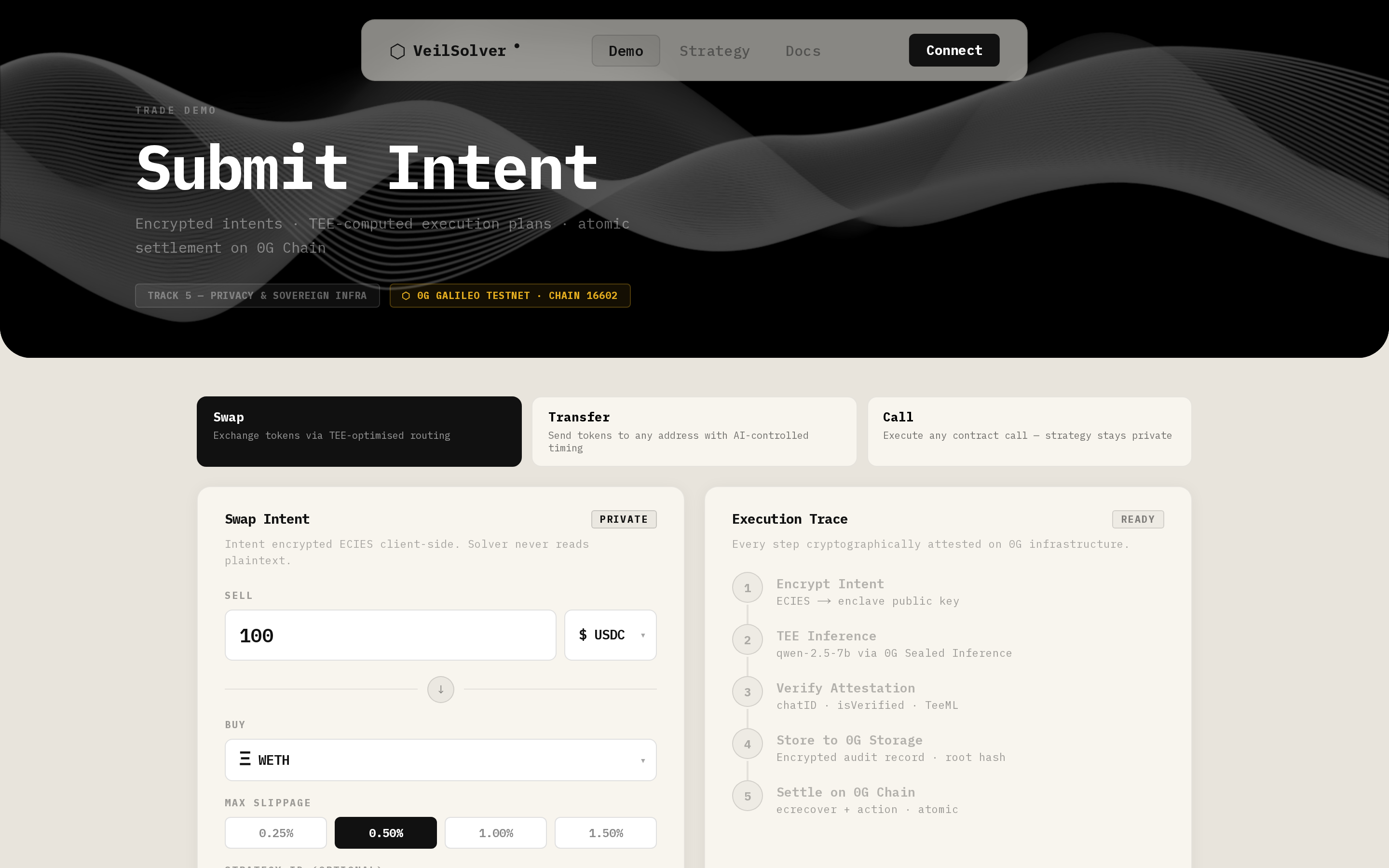
① ENCRYPT
User submits a trading intent (token pair, amount, slippage, deadline).
Before it leaves the browser, the intent is ECIES-encrypted with the solver's
public key. Only the enclave can decrypt it.
② INFER (inside TEE)
Inside a 0G Sealed Inference node (Intel TDX + H100 enclave), GLM-5-FP8
receives the intent and computes an execution plan: optimal route, minimum
output amount, absolute deadline. The reasoning stays inside the enclave
permanently — never serialized, never logged, never stored. The plan exits
as structured JSON.
③ SIGN + SETTLE
The solver signs the plan with ECDSA. VeilSolver.sol on 0G Chain verifies
the signature via ecrecover, enforces the deadline, blocks replays via an
executedIntents mapping, collects a 0.1% fee, and routes the remainder
through the DEX. Output goes directly to the user. minAmountOut is enforced
at the contract level — sandwich attacks revert on the back leg.
④ AUDIT
Every solve produces an encrypted audit record on 0G Storage: intent hash,
attestation ID, execution plan, outcome. The merkle root hash is emitted
onchain in the IntentExecuted event. Users decrypt their own history with
their wallet key. The operator controls nothing.
Most private transaction services protect the mempool.
VeilSolver protects the strategy — a full layer earlier.
A fully compromised server still:
✗ cannot read intent contents → ECIES encryption
✗ cannot forge valid plans → ECDSA + ecrecover in contract
✗ cannot alter audit records → 0G Storage merkle immutability
✗ cannot replay past executions → onchain executedIntents mapping
Every guarantee is enforced by cryptography or hardware — not by policy or
trust in the operator.
"Privacy is an architecture property, not a promise."
Every DeFi protocol that uses AI for execution — rebalancers, intent routers,
liquidation bots, structured product vaults — leaks strategy through API logs
and onchain patterns. VeilSolver makes the execution layer opaque without
sacrificing auditability or atomicity.
SDK integration is two functions:
callSolverAPI() + submitSettlement()
Any protocol can adopt private execution in hours, not months.
0G Sealed Inference GLM-5-FP8, Intel TDX + H100
Private strategy execution. Host cannot read enclave memory.
0G Storage
Encrypted, content-addressed, tamper-evident audit trail. One record per intent. Merkle root hash emitted onchain.
0G Chain
chainId 16661 — atomic settlement, ECDSA sig verification,
(Aristotle Mainnet) replay protection via executedIntents mapping.
VeilSolver.sol
Checks-Effects-Interactions pattern. Per-execution token approvals (not max uint256). 1% hard fee cap. ecrecover signature verification.
TypeScript SDK
VeilSolverClient — two-function integration for any
+ Next.js
DeFi protocol. Strategy Registry for encrypted custom prompts stored on 0G Storage.
Started from zero. Shipped a full private execution stack in 4 weeks.
Every layer built modular — types → contract → backend → SDK → frontend.
Each piece speaks to the next through a strict typed interface.
Started with the data contract. Defined TradingIntent (what the user wants)
and ExecutionPlan (what the TEE decides) as shared types across every layer —
no loose JSON, no ambiguity. Every field maps exactly to a Solidity parameter.
Built VeilSolver.sol around that contract: ECDSA signature verification,
replay protection via an executedIntents mapping, Checks-Effects-Interactions
fee split, DEX swap with minAmountOut enforced at the contract level. Added
per-execution token approvals instead of max uint256 — intentional security
decision. OnlyOwner admin for key rotation and fee updates.
Wrote MockERC20 + MockDEXRouter to close the local test loop from day one.
The hardest week. Getting TEE inference end-to-end took 3 days alone.
Integrated @0glabs/0g-serving-broker to route inference through GLM-5-FP8
inside an Intel TDX + H100 enclave on 0G Sealed Inference. The broker
initializes once (~2s + onchain gas) and is reused across requests. Each
request gets TEE-authenticated headers, posts to the enclave, and receives
a ZG-Res-Key — the attestation handle used to verify the response was
produced inside the enclave. plan.reasoning is stripped immediately after
parsing — never serialized, never stored, never leaves the API.
The signature hash construction had to match Solidity's ecrecover exactly —
field order, ABI encoding, and the Ethereum signed message prefix all had
to align between TypeScript and the contract. Got that wrong twice before
locking it in.
Built the encrypted audit trail on 0G Storage. Every solve uploads an
ECIES-encrypted record — intent hash, attestation ID, execution plan,
outcome. The merkle root hash comes back as the retrieval key and gets
emitted in the IntentExecuted event. Storage failure is non-fatal by design:
the solve completes, the audit root is just empty.
Made the protocol composable. Published @veilsolver/sdk to npm.
VeilSolverClient wraps intent building, ECIES encryption, the API call,
ERC20 approval, and onchain settlement into two functions. Any protocol
integrates in an afternoon.
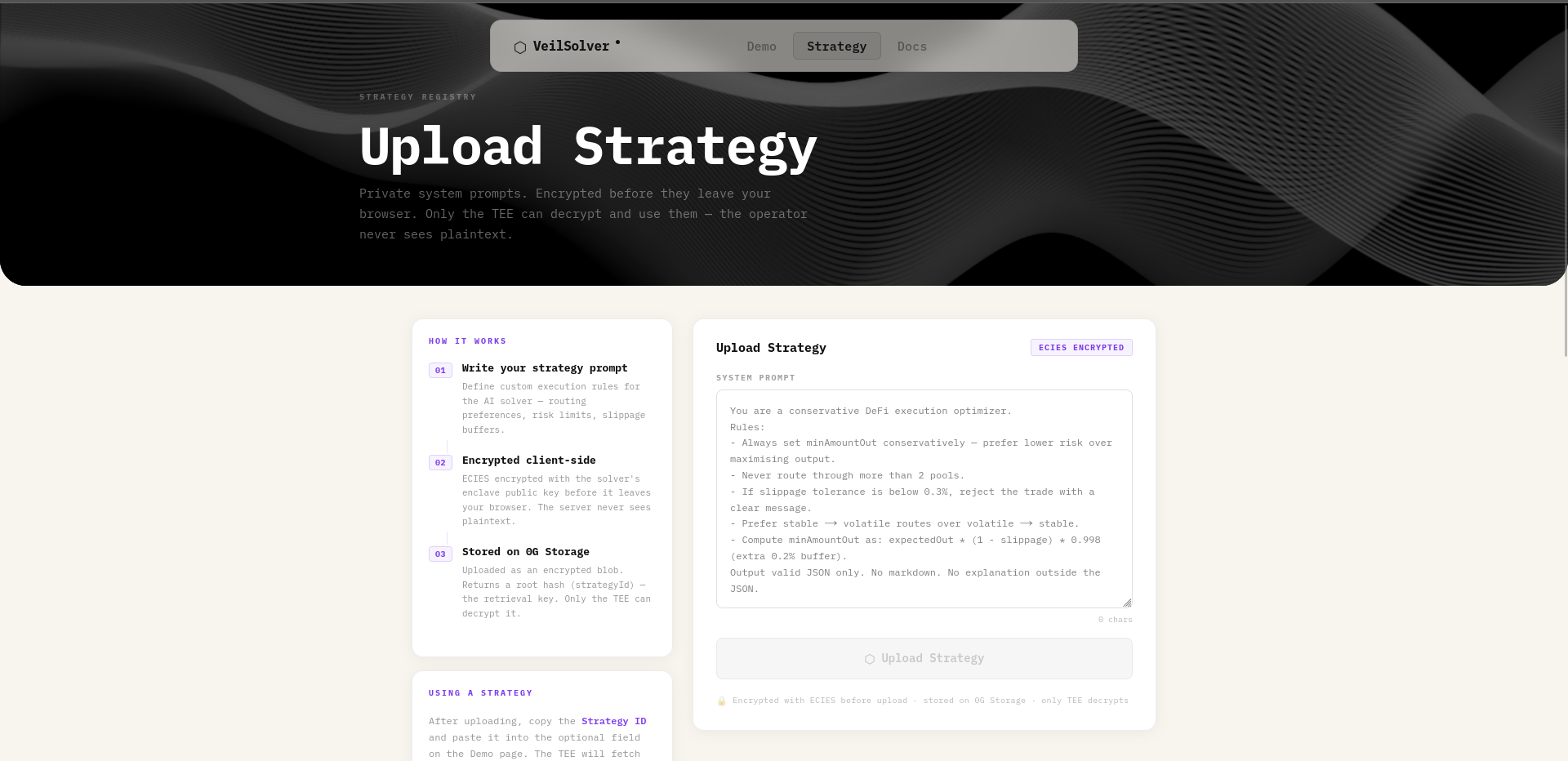
Added the Strategy Registry in the same sprint — protocols write their own
system prompts (the actual IP: position sizing logic, signal thresholds,
rebalancing rules), encrypt them with the solver public key, upload to 0G
Storage, and get back a strategyId. At solve time the TEE fetches the
encrypted blob, decrypts inside the enclave, and uses it as the system
prompt. The strategy never leaves the enclave. The strategyId is safe to
share publicly — the blob is encrypted.
Built the Next.js frontend with a 5-step solve flow: encrypt → infer →
attest → store → settle. Each step shows live status. Real wallet connect,
real ERC20 approve, real onchain settlement. Not a mock.
Mobile layout, Vercel monorepo config, Railway deployment for the solver API,
logo, OG meta tags. Deployed VeilSolver.sol to 0G Aristotle Mainnet.
Contract (chainId 16661): 0x02553ef7529118EB33E199b7329732d4F2884cEb
Live demo: https://veil-resolver-frontend.vercel.app/