Private eligibility firewall on 0G. Workers prove eligibility for free legal help without disclosing name, HKID, employer. Subpoenas reach only a 15-min timestamp bucket. Live on Aristotle mainnet.

**368,000 foreign domestic helpers in Hong Kong — 9.6% of the workforce. 17% in forced labour. 60% deterred from filing Labour
Tribunal claims by deportation fear. Every legal-aid intake forces disclosure of name, HKID, employer — every disclosure
subpoena-reachable. Compass fixes this. Live on 0G Aristotle mainnet (chainId 16661).**
## The asymmetry
Migrant workers in Hong Kong number 368,000 — 9.6% of the local workforce (HK LegCo Research Office, 2025). Across APAC, 27.2
million migrant workers face similar disclosure traps (ILO Global Estimates, 2024). The services that exist to help them —
legal aid clinics, shelters, public hospitals — all require identifying information at intake. Name, HKID, employer, visa
status. Those are exactly the fields an abusive employer can later subpoena, or that a trafficker can use to find a worker who
sought help. The status quo asks the most vulnerable people in the system to choose between getting help and being safe.
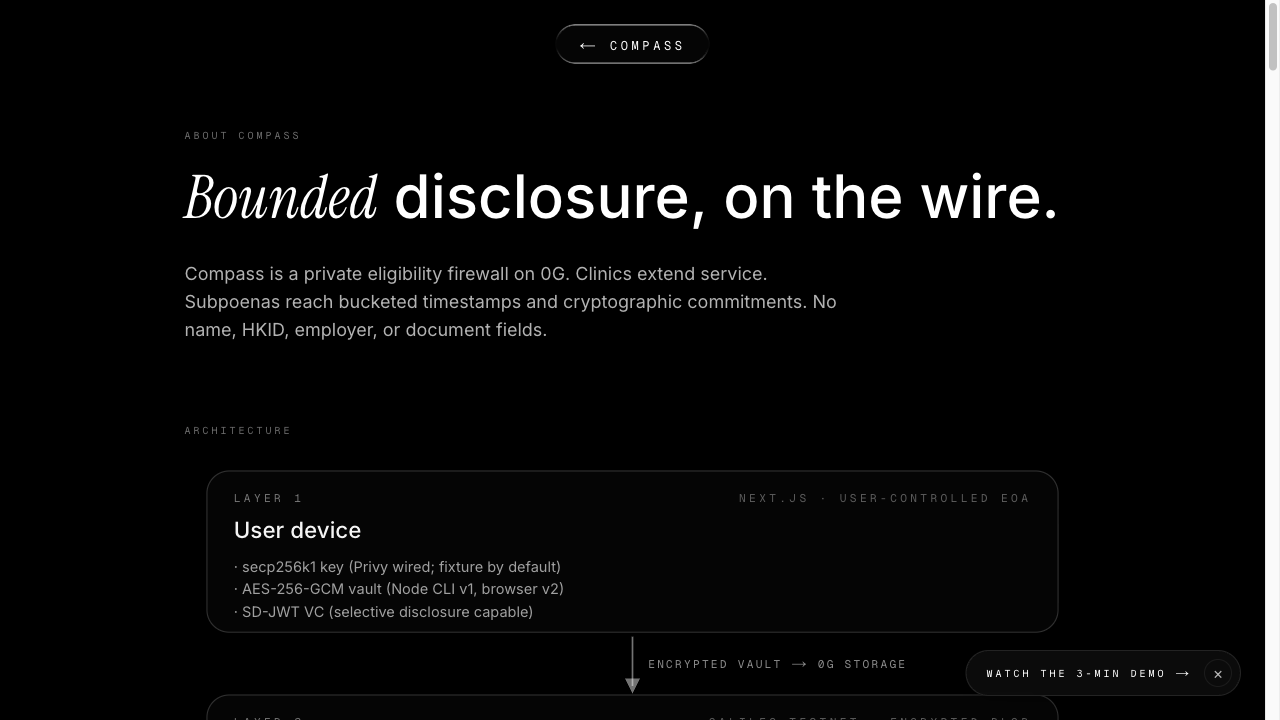
## What Compass changes
Compass eliminates the disclosure. A vulnerable worker carries an encrypted SD-JWT verifiable credential in her browser vault.
A sealed inference receipt-signer running inside a Phala dstack TDX trusted execution environment evaluates an eligibility
policy against selectively-disclosed claims. The result lands on 0G Chain as a ReceiptIssued event whose fields are
non-identifying — only a 15-minute timestamp bucket, a policy ID, a nullifier, and a cryptographic commitment to the agent's
on-chain identity.
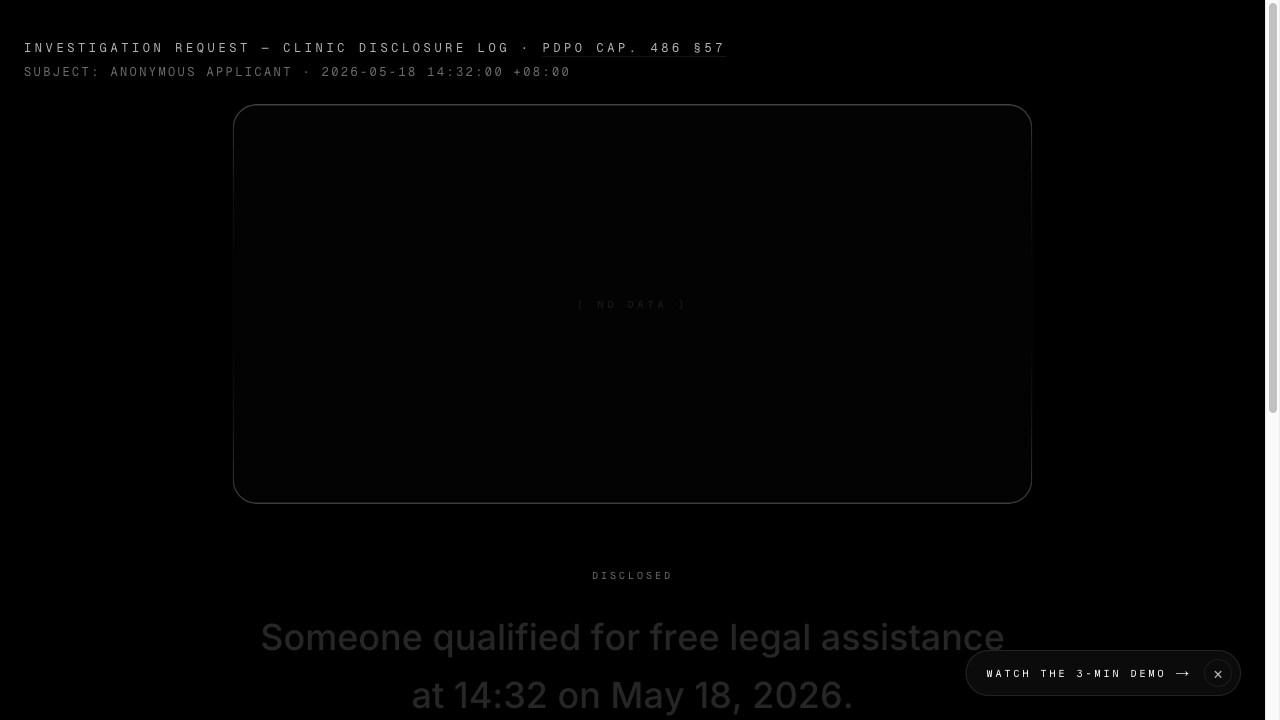
A subpoena reaches the timestamp bucket and the commitment. Nothing else exists to be disclosed.
## How it's built
Compass runs end-to-end on 0G:
- 0G Chain (Aristotle mainnet 16661 + Galileo testnet 16602) — AgentRegistry holds a soulbound INFT bound to the user's EOA.
CompassHub atomically consumes a single-use grant and issues a receipt in one transaction; nullifier-replay and
receipt-id-replay protection both enforced on-chain.
- 0G Storage — the user's SD-JWT VC ciphertext (AES-256-GCM with a non-extractable WebCrypto key in IndexedDB) is uploaded to
0G Storage; the Merkle root is committed to AgentRegistry.encryptedURI. The decryption key never enters the chain.
- 0G TeeML / Phala dstack TDX — the receipt-signer derives a deterministic secp256k1 key sealed to its attested image via
dstack.getKey('compass-receipt-signer'). Each receipt is bound to a per-receipt RA quote whose report_data commits to (signer,
image, receiptId), defeating archived-quote replay across deployments.
## Honest limits
We are explicit about what Compass does NOT do. Coercion: an abusive employer who can see the worker's screen at disclosure
can still read the plaintext SD-JWT VC before encryption. Coarse buckets: 15-minute windows are not full k-anonymity against
statistical re-identification in edge cases. SD-JWT VC draft churn: the implementation pins to draft-15; we'll roll forward as
the standard finalises. Full list at docs/honest-limits.md.
## What's verifiable today
- 40 Hardhat unit tests + property-based invariants pass.
- 103 receipt-signer vitest tests pass.
- Slither 0.11.5 with 101 detectors: 0 security findings.
- Codex GPT-5.5 adversarial pre-submission review caught + fixed 1 BLOCKER before mainnet deploy.
- 5 prior security audits (Codex x3, Slither, ultrareview, OWASP API).
- Playwright E2E suite scaffolded across the user journey.
Don't trust the maintainer — re-derive the cryptographic chain yourself with `enclave/src/verify-receipt.ts --bundle
<receipt.json>`.
## Business Impact
TAM — 368,000 FDHs in Hong Kong (LegCo 2025) + 27.2M migrant workers across APAC (ILO 2024). HK Legal Aid Department spent
HK$679.6M on civil cases in FY2024/25 — none of it prevents the disclosure that triggers deportation.
Cost per incident:
- Worker side: ≈ US$22,200 lost (HK$152K remaining contract wages + HK$21K outstanding recruitment debt).
- Hong Kong government side: ≈ US$14,100 lost (≈ HK$71,500 LAD civil application + HK$40-60K deportation processing).
Sustainability — open-source. Free for migrant-worker NGOs. AGPL core + commercial dual-license for non-NGO deployments.
Phala dstack TDX hosting costs ≈ US$15/year per receipt-signer instance. 12-month grant ladder mapped: Phala Builders Program
($10-50K) → 0G ecosystem ($10-100K) → EF PSE + Mozilla Technology Fund ($30-250K) → Open Society Migration Initiative +
Luminate + HK Jockey Club Special Projects ($150K-1M+). Target by month 18: ≈ US$60K/year recurring (managed hosting +
dual-license), reducing grant dependency below 60%.
Full numbers + sources in [docs/whitepaper.md → §Business
Impact](https://github.com/StephenSook/Compass-OG-/blob/main/docs/whitepaper.md#business-impact).
## Try it
- Live frontend: https://app-psi-pied.vercel.app
- Subpoena scene: https://app-psi-pied.vercel.app/clinic/subpoena
- Public audit log: https://app-psi-pied.vercel.app/audit
- 3D audit visualization: https://app-psi-pied.vercel.app/audit-graph.html
- Repo: https://github.com/StephenSook/Compass-OG-
- Demo video: https://www.youtube.com/watch?v=vg5WZHmlzZI
- Whitepaper PDF: https://github.com/StephenSook/Compass-OG-/blob/main/docs/whitepaper.pdf
Built solo by Stephen Sookra for the 0G APAC Hackathon Track 5 (Privacy & Sovereign Infrastructure).
Built end-to-end during the 0G APAC hackathon window (project kickoff 2026-05-02; submission 2026-05-16).
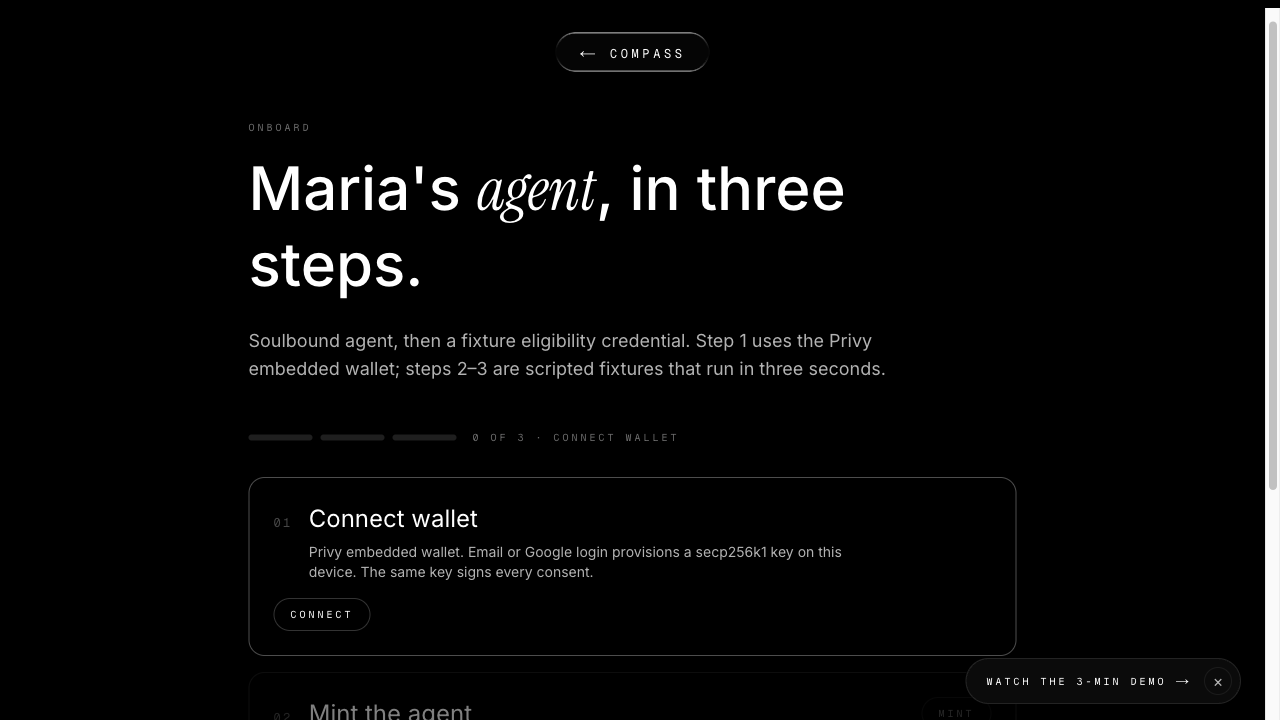
Phase A — credential vault + agent identity (May 2-3)
Browser-side AES-256-GCM encryption with non-extractable WebCrypto keys in IndexedDB. SD-JWT VC draft-15 selective disclosure.
Soulbound minimal INFT on AgentRegistry binding the user's EOA to their encrypted vault URI on 0G Storage.
Phase B — TEE receipt-signer (May 4-5)
Express service running inside a Phala dstack TDX CVM. Deterministic secp256k1 key derivation via
dstack.getKey('compass-receipt-signer'). Per-receipt RA quote with `report_data = sha256(signer || composeHash ||
receiptId)` — defeats archived-quote replay across deployments. ADR-003 documents the binding rationale.
Phase C — atomic on-chain consume + issue (May 5-6)
CompassHub.consumeGrantAndIssueReceipt() consumes a single-use grant and emits ReceiptIssued in one transaction.
Nullifier-replay + receipt-id-replay protection enforced on-chain. 40 Hardhat unit tests + property-based invariants pass.
Phase D — subpoena scene + audit log (May 7-8)
/clinic/subpoena page renders what a clinic could actually disclose under PDPO §57 — only the 15-min timestamp bucket and the
receipt commitment exist. /audit page lists every on-chain receipt with no identifying fields. /audit-graph.html renders the
audit log as a 3D force-graph.
Phase E — Aristotle mainnet deploy (May 10)
AgentRegistry at 0xf1FAaBef1d00Db1a15b7637Dc0d8526449D06Bf9 and CompassHub at 0xe42fd4F0a3197126fEeF5e6AAfC5Fb8848bBC58b on 0G
Aristotle mainnet (chainId 16661). 3 demo policies (HELP / Bethune / HK FDH Hospital) registered on-chain.
Phase F — demo + submission (May 11-16)
Three-minute demo video at https://www.youtube.com/watch?v=vg5WZHmlzZI. Mermaid C4Context architecture diagram. 3 ADRs
(MADR-lite) covering platform / credential / quote-binding decisions. Multi-agent audit landed CRITICAL Privy SSR fix + Docker
dependabot + network-copy corrections. Final-week X cadence locked.
Verifiability ledger (what shipped, what's testable):
- 40 Hardhat unit tests + property-based invariants ✓
- 103 receipt-signer vitest tests ✓
- Slither 0.11.5 (101 detectors): 0 security findings ✓
- Codex GPT-5.5 adversarial review: 1 BLOCKER caught + fixed pre-mainnet
- 5 prior security audits (Codex x3, Slither, ultrareview, OWASP API)
- Playwright E2E suite scaffolded across user journey
- Verifiable independence: enclave/src/verify-receipt.ts --bundle <receipt.json> lets anyone re-derive the cryptographic
chain offline.
Non-code surfaces shipped: README ToC + Mermaid C4 architecture diagram · 3 ADRs (MADR-lite: platform / credential /
quote-binding) · whitepaper PDF · press kit · 6 NGO outreach drafts (HELP, Bethune, Mission, Open Society, Luminate, Jockey
Club) · DoraHacks + Devpost cross-listing drafts.
Not actively fundraising. Solo hackathon build.
Open post-deadline to:
- Ecosystem grants (0G Foundation, Ethereum Foundation Privacy & Scaling Explorations, Phala Network ecosystem fund)
- NGO partnerships in the HK migrant-worker space (Bethune House, HELP for Domestic Workers, Mission for Migrant Workers, Open
Society Foundations)
- v0.6 roadmap funding: native-speaker localization review (Filipino, Bahasa Indonesia, Bahasa Malaysia, Cantonese),
browser-side 0G Storage upload v2, Mythril symbolic-execution audit pass
6 cold-outreach drafts queued at docs/outreach/ ready to send after May 16.