Fraudify
Real-time Web3 threat detection
Videos
Tech Stack
Description
FRAUDIFY — Decentralized AI-Powered Transaction Security
Bittensor Subnet Ideathon · Real-time Web3 threat detection, powered by decentralized AI
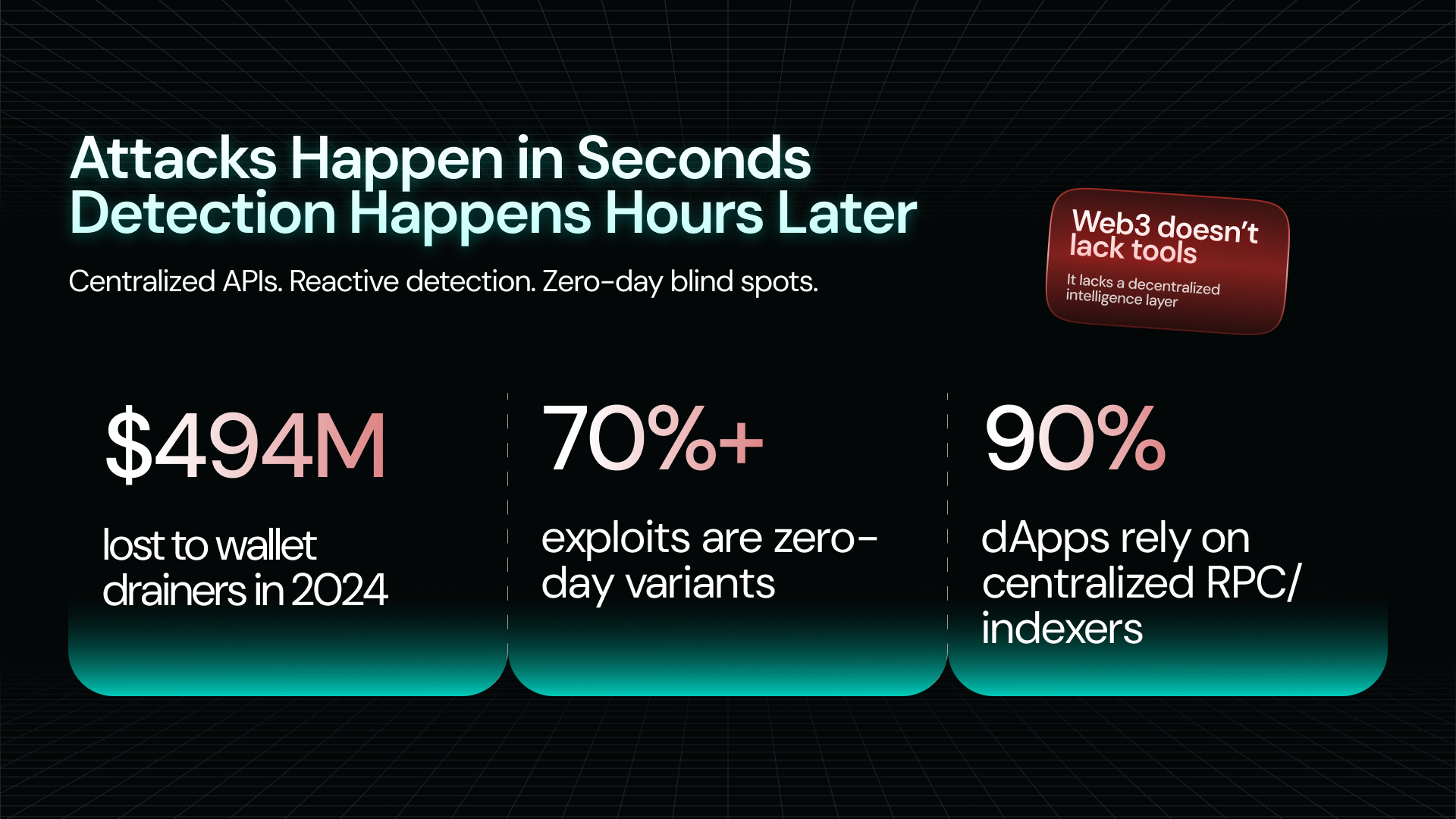
The Problem
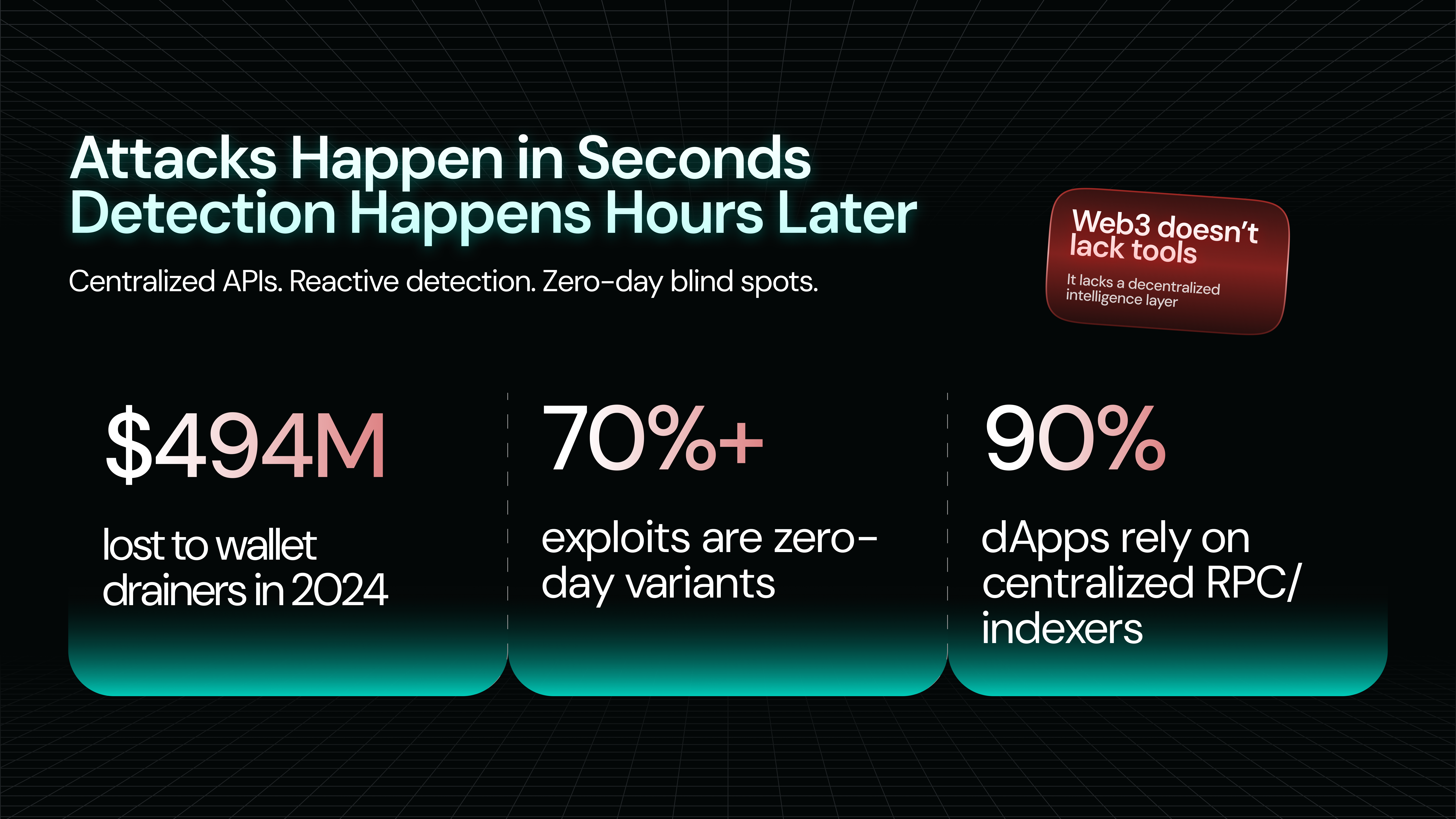
Every day, crypto users lose millions to drainer contracts, phishing signatures, honeypot tokens, and flash loan attacks. Existing security tools share the same fatal flaw: they're too slow, too centralized, or too dumb.
Blacklist databases take 24–48 hours to update after an attack is discovered — by then, dozens of victims are already drained.
Centralized simulation APIs (Blowfish, Tenderly) are a single point of failure. One outage, and millions of wallets go blind.
Rule-based detection can't learn. It only catches attacks it has already seen.
Enterprise security stacks cost $300K–$800K/year — completely out of reach for 90% of protocols.
The result: users sign malicious transactions every single day, with no effective warning.
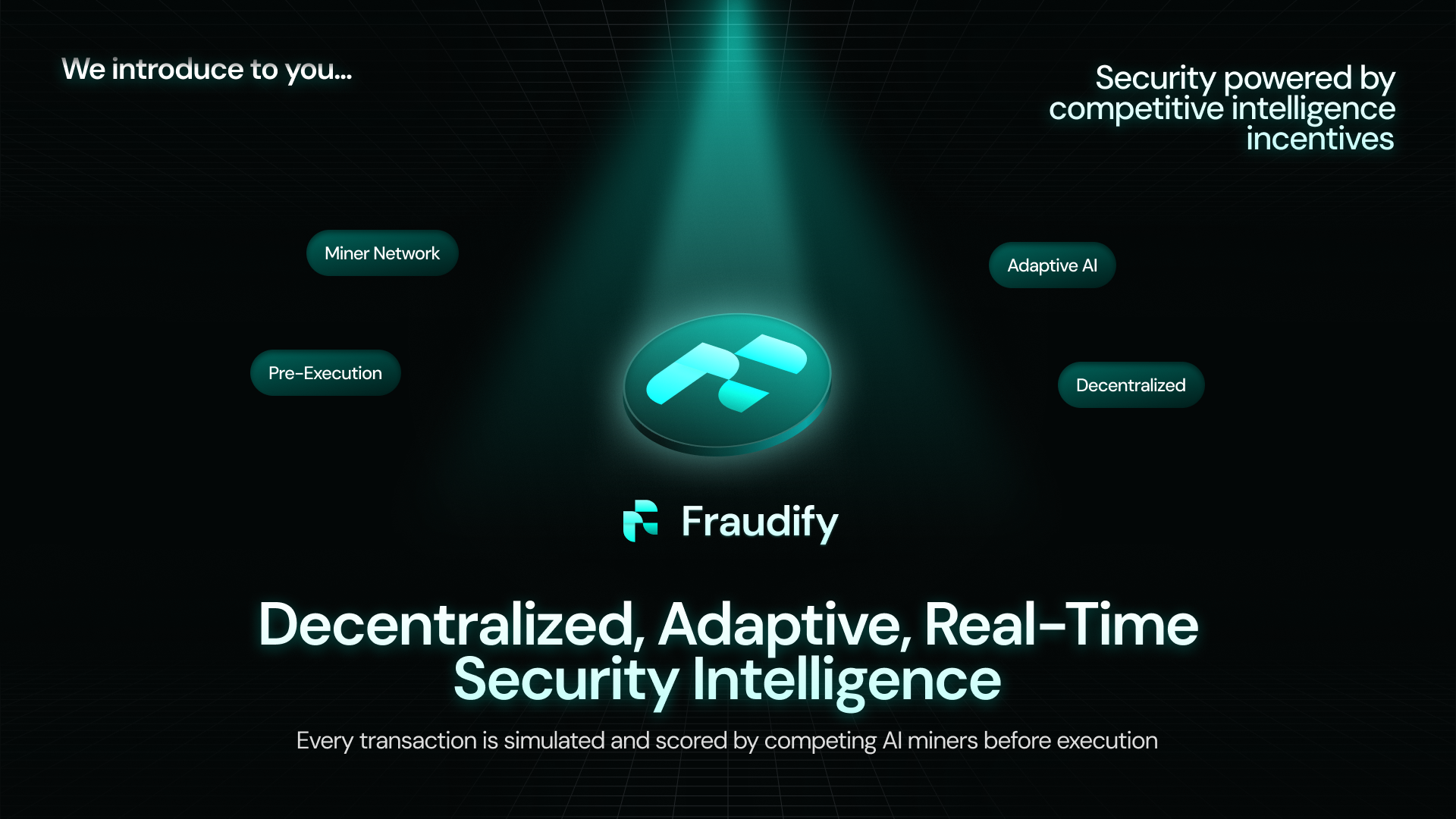
The Solution: Proof of Intelligent Simulation
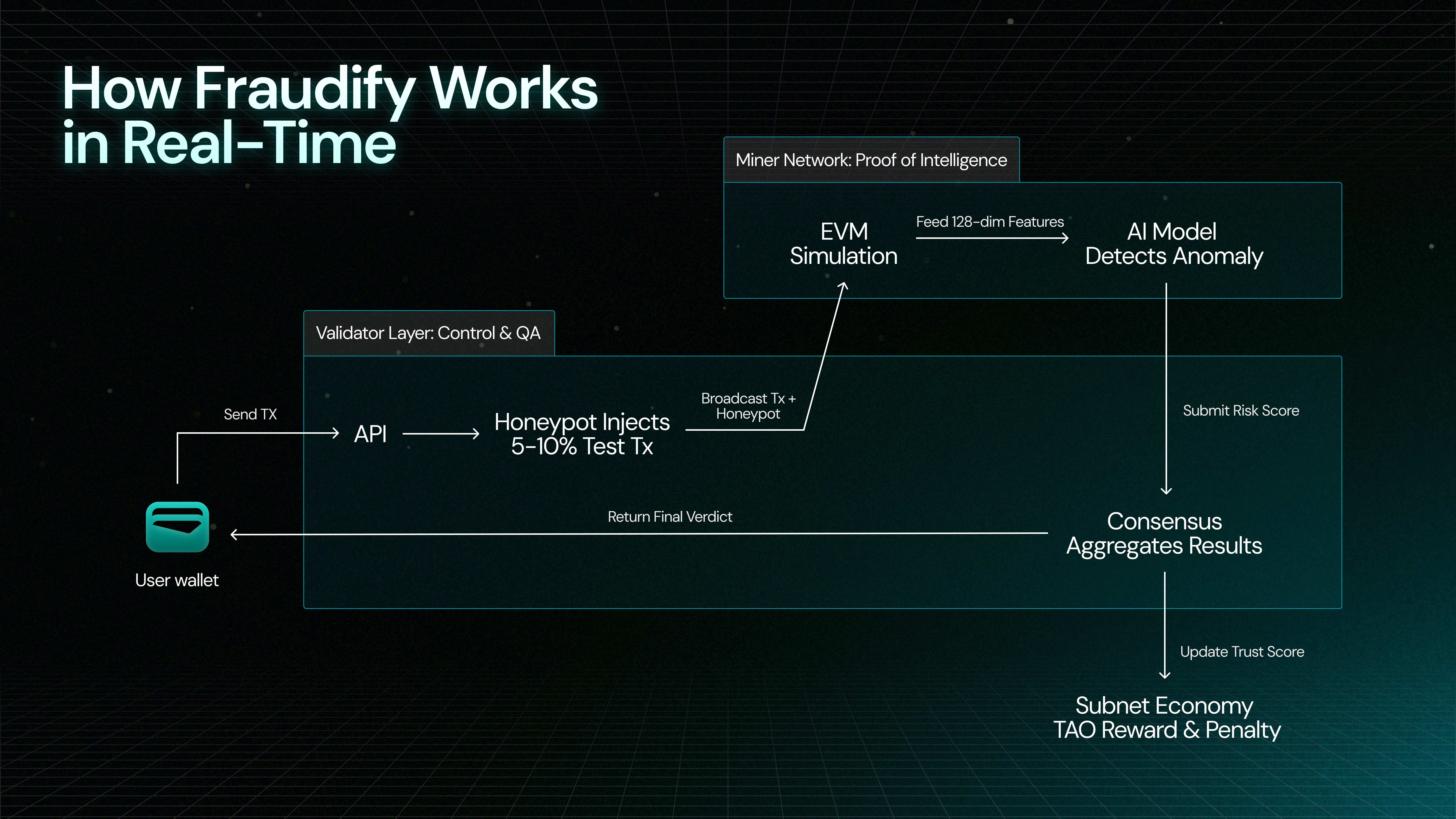
Fraudify is a Bittensor subnet that turns transaction security into a competitive AI marketplace. Instead of relying on a single provider, Fraudify deploys a decentralized network of miners that each:
Simulate the transaction in a sandboxed EVM — seeing exactly what would happen before you sign.
Analyze the result with a trained ML anomaly detection model — detecting attack patterns, even zero-day ones.
Return a risk verdict with human-readable explanations in under 500ms.
Miners compete to deliver the most accurate analysis. Better AI models = higher TAO rewards. The network gets smarter over time — automatically.
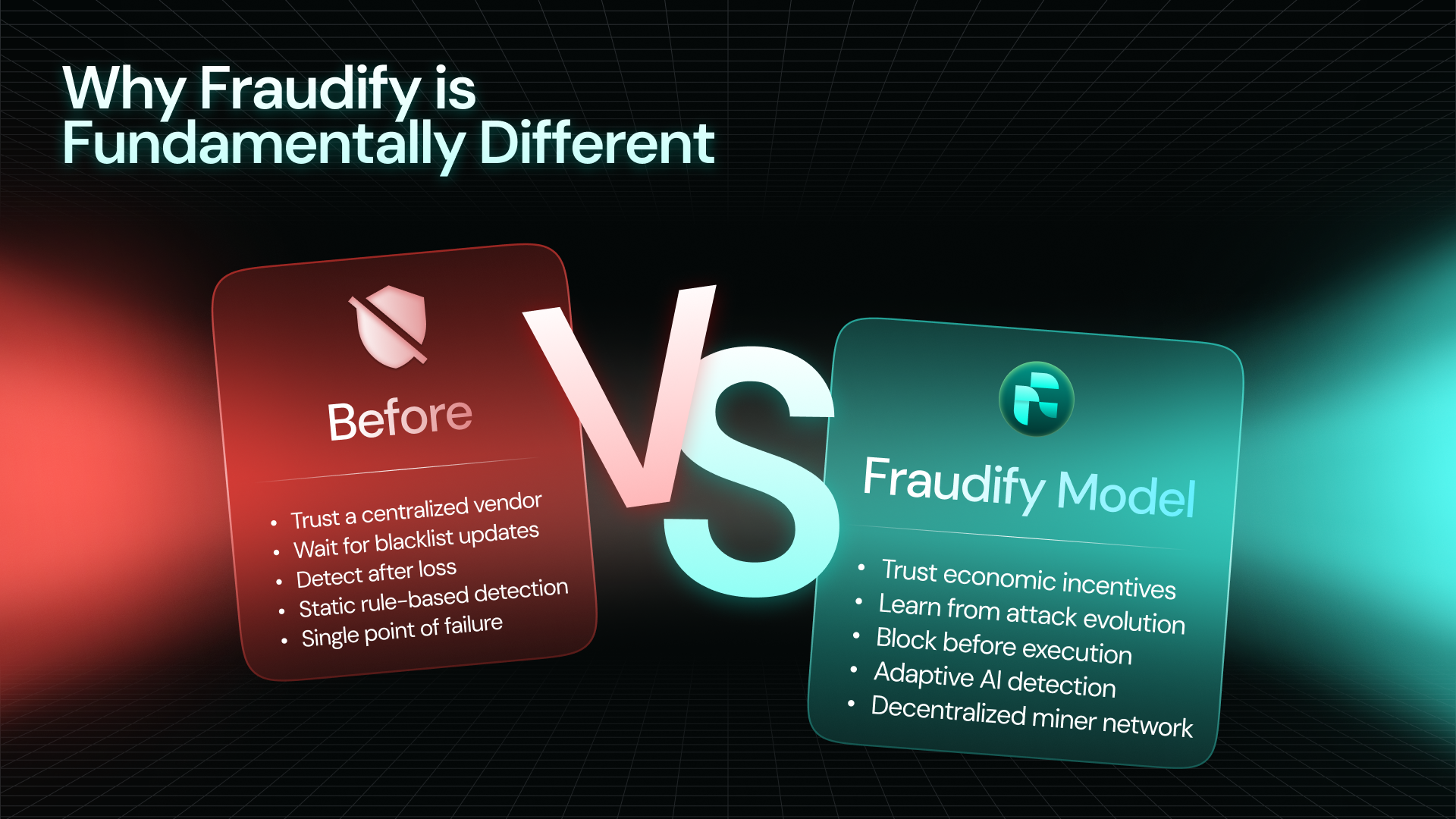
Why This Is Different
Solution | Monthly Cost (50K tx) | AI Detection | Decentralized |
|---|---|---|---|
Blowfish API | $2,000–$5,000 | ❌ | ❌ |
Tenderly | $1,000–$3,000 | ❌ | ❌ |
In-house team | $20,000+ | Custom | ❌ |
Fraudify | $500–$1,000 | ✅ | ✅ |
Built on Bittensor — By Design
Fraudify isn't just using Bittensor — it's designed around it. EVM simulation and AI inference are computation-intensive, variable in quality, and highly parallelizable: a perfect fit for Bittensor's incentive model where intelligence is the commodity.
The subnet introduces a novel Honeypot Anti-Gaming Mechanism: validators inject transactions with known outcomes to continuously verify miner honesty and accuracy. No shortcuts. No freeloading.
The Opportunity
The Web3 security market is underserved, growing, and structurally broken. Fraudify enters as a drop-in API for any wallet or DApp, with a clear path from free-tier adoption → DeFi partnerships → enterprise SLA contracts.
Curious about the full architecture, incentive model, and go-to-market strategy?
→ Read the full whitepaper to see how Fraudify works under the hood.
Progress During Hackathon
During this hackathon, the Fraudify team has completed a full subnet design proposal covering all core components of the protocol. Here's a summary of what was accomplished:
✅ Research & Problem Validation
Analyzed existing Web3 security solutions (Blowfish, Tenderly, Forta, Pocket Universe) and documented their structural limitations
Identified four root causes of the current security crisis: latency gaps, centralization risks, cost barriers, and intelligence limitations
Validated the market opportunity — 90% of protocols cannot afford enterprise security stacks
✅ Protocol Architecture Design
Designed the Proof of Intelligent Simulation (PoIS) consensus mechanism combining EVM simulation with ML anomaly detection
Defined the full Miner pipeline: input format, 4-step processing pipeline, 128-dimension feature extraction, and output format
Designed the Validator system including request distribution, result aggregation, and the Honeypot Anti-Gaming Mechanism
✅ Incentive & Economic Model
Defined TAO emission distribution (60% miners / 30% validators / 10% subnet owner)
Designed multi-dimensional miner scoring formula (accuracy 40%, speed 30%, reliability 30%)
Designed tiered penalty system with four levels: minor, moderate, major, and critical (ejection)
Modeled the business revenue structure and competitive pricing against existing alternatives
✅ Technical Specifications
Defined full API specification (endpoints, rate limits, authentication)
Produced SDK integration examples in TypeScript and Python
Specified AI model architecture (~100K parameters, lightweight for fast inference)
Documented 10 anomaly types and 5 attack pattern categories for detection
✅ Go-To-Market Strategy
Designed a 3-phase GTM plan (wallet integrations → DeFi expansion → enterprise market) with concrete adoption targets
Defined miner and validator bootstrapping incentives for network cold-start
Produced a 12-month implementation roadmap with milestones
Fundraising Status
Stage: Pre-seed / Bootstrapped
Fraudify is currently self-funded by the founding team and has not raised external capital. The project is at the ideation and design phase, with this hackathon being the first public milestone.
We are actively looking for:
Ecosystem grants — Bittensor / Opentensor Foundation grants to fund initial subnet deployment and model training
Angel investors — Individuals with Web3 security or Bittensor ecosystem experience
Strategic partners — Wallet teams, DeFi protocols, or security-focused DAOs interested in early-stage collaboration
If you are interested in supporting Fraudify's development, we welcome conversations at any stage.