SealedMind
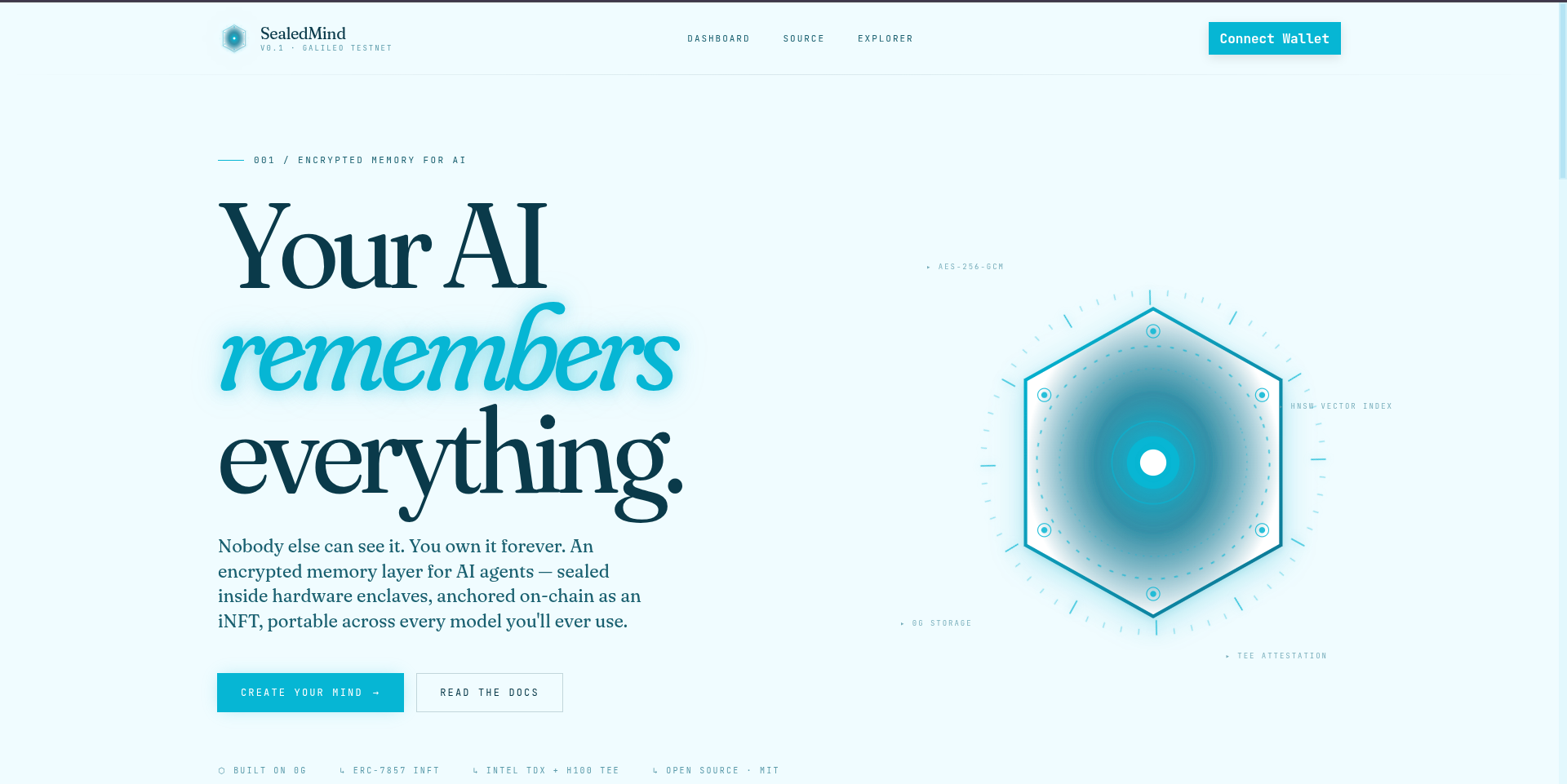
We built a memory layer for AI encrypted, portable, and provably secure. Your AI remembers everything. Nobody else can read it. You own it forever.
Videos
Tech Stack
Description
What is SealedMind?
SealedMind is a privacy-first AI memory layer built on the 0G ecosystem. It gives every user a sovereign, encrypted, AI-searchable memory vault — called a Mind — that no one, not even the application, can read without explicit consent. Think of it as a personal second brain that lives on a decentralized network, processed inside a hardware-level trusted execution environment, and owned entirely by the user's wallet.
The Problem
AI assistants today accumulate deeply personal knowledge about users health conditions, financial situations, relationships, daily habits. But all of this is stored in plaintext on centralized servers controlled by companies. Users have no ownership over their data, no way to audit who accessed it, no way to selectively share specific parts with specific apps, and no way to take it with them if they switch platforms.
The Solution
SealedMind fixes this by combining four technologies from the 0G ecosystem into a single privacy stack.
Every memory is encrypted client-side with AES-256-GCM before it ever leaves the user's device. The encrypted blob is then uploaded to 0G Storage where it lives permanently, identified by a content hash. On the 0G chain, an ERC-7857 iNFT called a Mind NFT is minted for each user this token is the on-chain identity that owns all the memory CIDs and controls who can access them. When a user wants to recall memories, the query goes through 0G Sealed Inference a Qwen 2.5 7B model running inside an Intel TDX enclave so the LLM processes the plaintext inside hardware-level isolation and the answer comes back with a cryptographic attestation proving it ran in a trusted environment. Plaintext never exists outside the enclave.
Smart Contracts
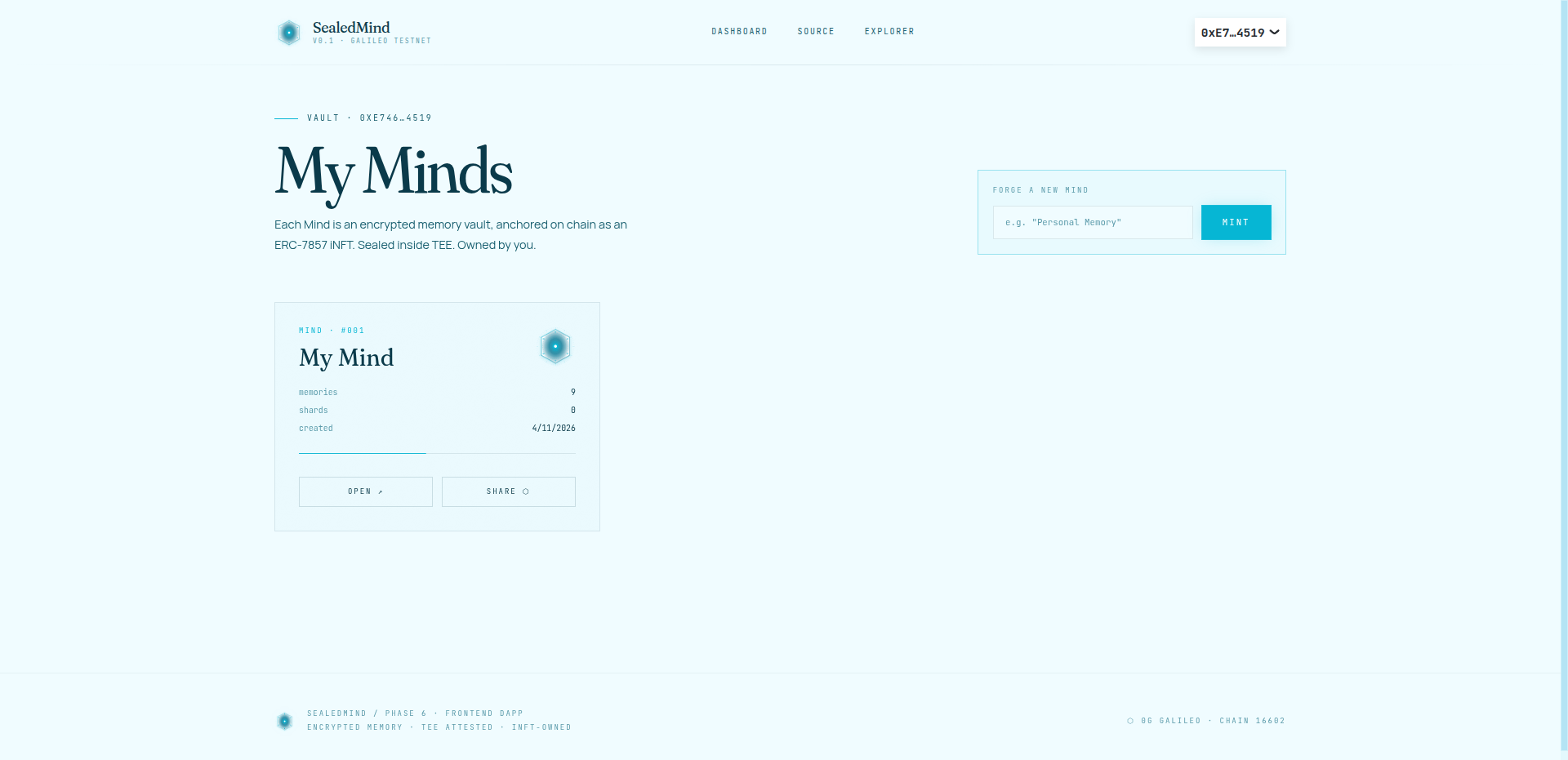
SealedMindNFT is an ERC-7857 intelligent NFT where one token represents one user's entire memory vault. It stores the 0G Storage CIDs, memory count, shard names, and the list of authorized users for each Mind.
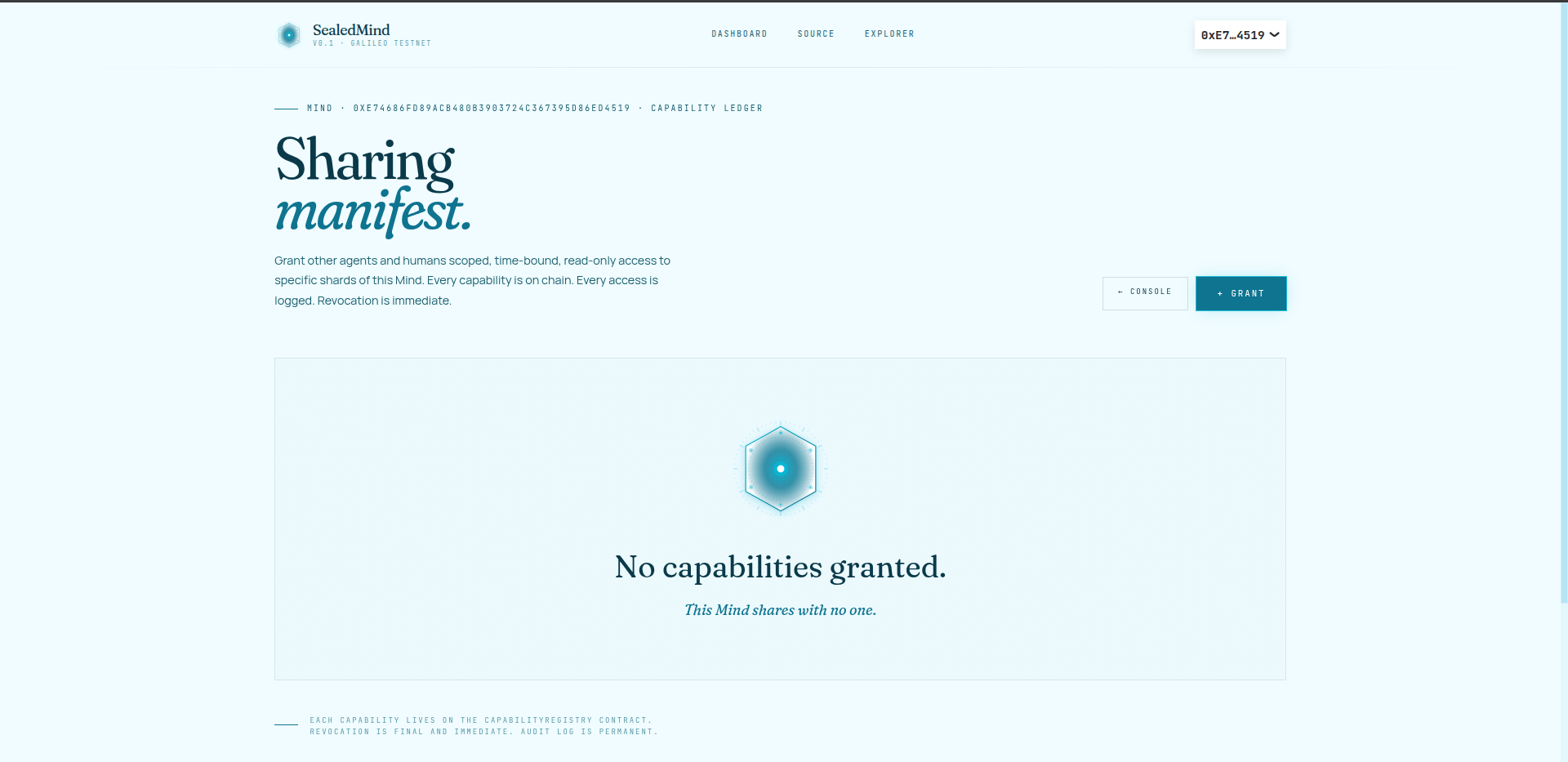
CapabilityRegistry lets Mind owners grant fine-grained access to specific memory shards — for example, granting a health app read-only access to the health shard while keeping finance and relationships private. Capabilities are on-chain, time-expiring, and revocable at any time.
MemoryAccessLog is an immutable on-chain audit trail that records every memory access event so users can always see exactly what was accessed and when.
Verifier is the TEE type verifier wired into SealedMindNFT for attestation validation.
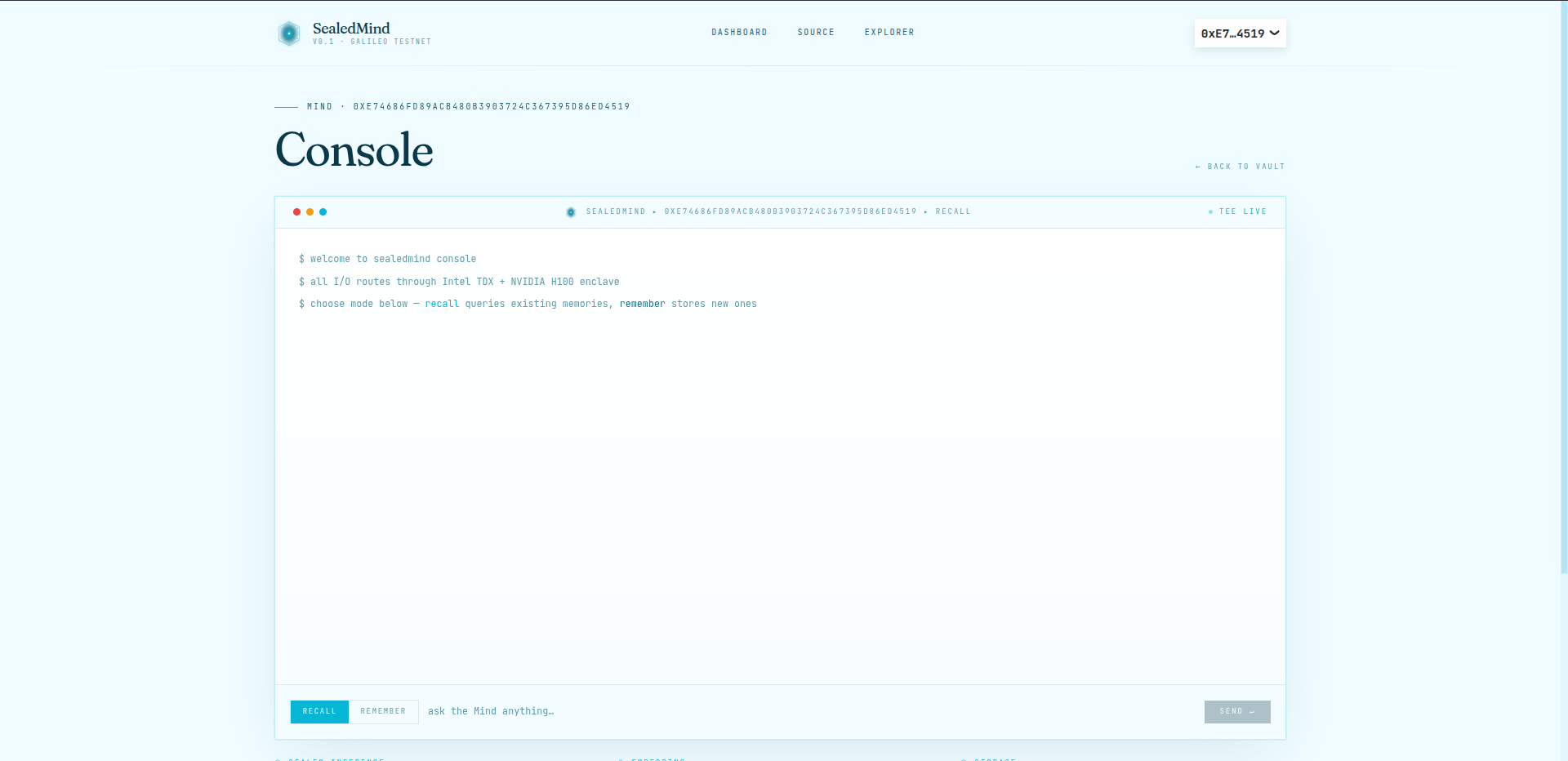
Backend
The backend runs on Node.js and Express. It handles Sign-In with Ethereum authentication, encrypts memories with AES-256-GCM, generates vector embeddings using HuggingFace all-MiniLM-L6-v2, stores encrypted blobs on 0G Storage, maintains an HNSW vector index for fast semantic similarity search, and routes recall queries through 0G Sealed Inference for TEE-attested synthesis.
Frontend
The React dApp uses Viem, Wagmi, and RainbowKit for wallet connection. Users can mint their Mind NFT, store memories organized into named shards like health, finance, work, and relationships, recall memories using natural language queries, and grant or revoke shard-level access to other wallet addresses — all on-chain. Every recall response displays a TEE attestation badge showing the response was generated inside a trusted enclave.
CLI and Agent
A Life OS agent built on OpenClaw and powered by Claude Haiku 4.5 lets users interact with their memory vault through natural conversation in the terminal. The agent automatically detects when something should be remembered, calls the sealedmind CLI to store it encrypted on 0G Storage, and recalls relevant memories when answering questions.
0G Technologies Used
0G Storage is used for all encrypted memory blob persistence. 0G Sealed Inference is used for TEE-attested fact extraction from raw text and for synthesizing recall answers from retrieved memories. 0G Chain is used for all smart contract interactions including Mind NFT minting, capability grants, revocations, and access logging.
Progress During Hackathon
Progress
Phase 0 — Project Scaffold
Set up a full monorepo with five packages: contracts (Hardhat), backend (Node.js/Express/TypeScript), frontend (React/Vite/TypeScript), sdk (TypeScript client library), and cli (command-line interface). Defined the full architecture ERC-7857 NFT identity, 0G Storage for encrypted blobs, 0G Sealed Inference for TEE processing, HNSW vector search for recall, and on-chain capability tokens for access control.
Phase 1 — Smart Contracts
Wrote and deployed four smart contracts to the 0G Newton Testnet (Chain ID 16602).
SealedMindNFT implements ERC-7857 the intelligent NFT standard where each token represents one user's encrypted memory vault. It stores 0G Storage CIDs, memory counts, named shards, and authorized user lists per token.
CapabilityRegistry implements on-chain capability tokens for shard-level access control. Mind owners can grant read or read-write access to specific shards with optional expiry timestamps. Capabilities can be revoked at any time and the revocation is enforced on-chain.
MemoryAccessLog provides an append-only on-chain audit trail. Every time a memory is accessed the event is logged immutably on the 0G chain.
Verifier is the TEE data verifier wired into SealedMindNFT for attestation. All four contracts were deployed in a single deployment transaction and the addresses were saved to a deployment manifest.
Contract Addresses on 0G Mainnet:
1.SealedMindNFT (ERC-7857): 0x091CfC4b9E6FF0026F384b8c4664B8C03Af21EA6
Explorer: https://chainscan.0g.ai/address/0x091CfC4b9E6FF0026F384b8c4664B8C03Af21EA6
2.CapabilityRegistry: 0xeb2F5C59A38F0f2339F5B399e4EDeF1FA834FA45
Explorer: https://chainscan.0g.ai/address/0xeb2F5C59A38F0f2339F5B399e4EDeF1FA834FA45
3.MemoryAccessLog: 0xec9321C66aD8D73FB8f8D80736e1b6C47570c5Ad
Explorer: https://chainscan.0g.ai/address/0xec9321C66aD8D73FB8f8D80736e1b6C47570c5Ad
4.Verifier: 0x6D5B3B81119F78366B767DB81C2dd6625d5648Af
Explorer: https://chainscan.0g.ai/address/0x6D5B3B81119F78366B767DB81C2dd6625d5648Af
Phase 2 — 0G Storage Integration
Built the storage service wrapping the 0G TypeScript SDK. Implemented AES-256-GCM encryption with random IV per blob, chunk-aligned padding (256-byte blocks with a 4-byte length header), upload to 0G Storage via the Indexer, and download with decryption and unpadding. Every memory blob is content-addressed by its rootHash which is stored in the Mind NFT on-chain.
Phase 2.5 — 0G Sealed Inference Spike
Investigated and resolved the @0glabs/0g-serving-broker ESM/CJS interop issue — the package ships a broken ESM build that re-exports from a CJS bundle, causing named import failures in Node.js ESM modules. Fixed by using createRequire from the Node.js module system to force the CJS import path. Validated the full TEE flow: broker initialization, provider discovery (listService → chatbot), metadata fetch, request header generation, inference call, and attestation verification via processResponse.
Phase 3 — Memory Engine
Built the full memory store and recall pipeline. For storing: raw text goes through the TEE LLM (0G Sealed Inference, Qwen 2.5 7B) for structured fact extraction, then embeddings are generated using HuggingFace all-MiniLM-L6-v2 (384 dimensions, runs locally), facts are encrypted and uploaded to 0G Storage, the HNSW index is updated with the new vectors, and the Mind NFT on-chain is updated with the new CID and memory count.
For recall: the query is embedded, HNSW cosine similarity search finds the top-K nearest memories, the retrieved memory texts are sent to 0G Sealed Inference for synthesis into a natural-language answer, and the response includes the chatId and attestation validity flag from the TEE processResponse call.
Phase 4 — REST API
Built the full Express REST API with six route groups. Auth routes handle SIWE nonce generation, signature verification, and JWT session issuance. Mind routes handle NFT existence checks, creation, and metadata retrieval. Memory routes handle store and recall operations. Sharing routes handle capability grant and revoke by calling the CapabilityRegistry contract. All protected routes require a valid JWT from SIWE authentication.
Phase 5 — TypeScript SDK
Built a typed TypeScript SDK that wraps the entire API surface into a SealedMind client class. Covers authentication (getNonce, verify, logout), mind management (getMind, createMind), memory operations (store, recall), and sharing (grantCapability, revokeCapability, listCapabilities). Published as @sealedmind/sdk within the monorepo workspace.
Phase 6 — React dApp
Built the full frontend dApp using React, Vite, Tailwind CSS v4, Wagmi, Viem, and RainbowKit. Features include wallet connection with MetaMask and WalletConnect support, SIWE sign-in flow, Mind NFT minting with on-chain transaction, dashboard for storing memories into named shards (health, finance, work, relationships, general), natural language recall with TEE attestation badge on every response, and a Sharing page for granting and revoking shard-level capabilities to other wallet addresses with on-chain enforcement.
Phase 7 — CLI and Life OS Agent
Built the sealedmind CLI with remember and recall commands that talk to the backend API. Built a Life OS agent on the OpenClaw agent framework powered by Claude Haiku 4.5. The agent understands natural language instructions, automatically stores memories by calling the CLI when the user mentions something worth remembering, and recalls relevant memories when answering questions. Also built a branded chat UI (arctic vault aesthetic) that proxies messages to the OpenClaw agent so it can be demoed in a browser.
Phase 8 — Production Deployment
Deployed the backend to Railway with a custom nixpacks.toml (Node 20, Python 3, gcc, gnumake for hnswlib-node native compilation). Configured health check endpoint and restart policy. Fixed Railway PORT injection. Deployed the frontend to Vercel with VITE_API_URL and VITE_WALLETCONNECT_PROJECT_ID environment variables. Resolved workspace package unavailability on Vercel by bundling the SDK source inline into the frontend repo. Fixed TypeScript erasableSyntaxOnly constraint by converting constructor parameter properties to explicit class fields.