slxc-7857
Implementation of the missing ERC-7857 Sealed Executor layer. AI agent execution enforced inside Intel TDX enclaves, with on-chain authorization checked before encrypted model data is fetched.
视频
技术栈
描述
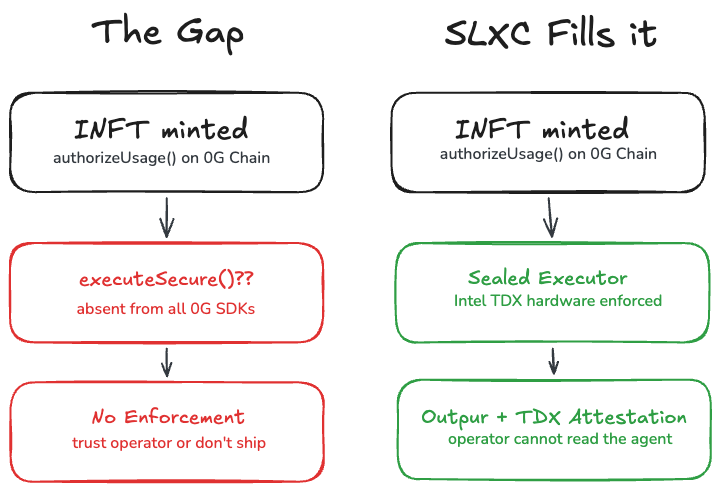
ERC-7857 defines authorizeUsage() for private AI Agent NFTs, but leaves the runtime that enforces it explicitly out of scope. 0G's own integration guide shows a function called executeSecure(), demonstrating how authorized subscribers invoke their agents. That function does not exist in any SDK, API, or GitHub repository across the entire 0G Foundation.
Sealed Executor Protocol
Sealed Executor Protocol is the first working implementation of the Sealed Executor as defined by ERC-7857.
The Core Bet
Build using the trust primitive the ecosystem already chose.
The operator cannot directly access the decrypted agent payload, because decryption occurs inside Intel TDX enclaves. Hardware enforcement, not operator promise.
How It Works
1. A creator encrypts their AI agent
2. The payload is stored on 0G Storage
3. An INFT is minted on 0G Chain with the storage reference
4. Subscribers are authorized on-chain via authorizeUsage()
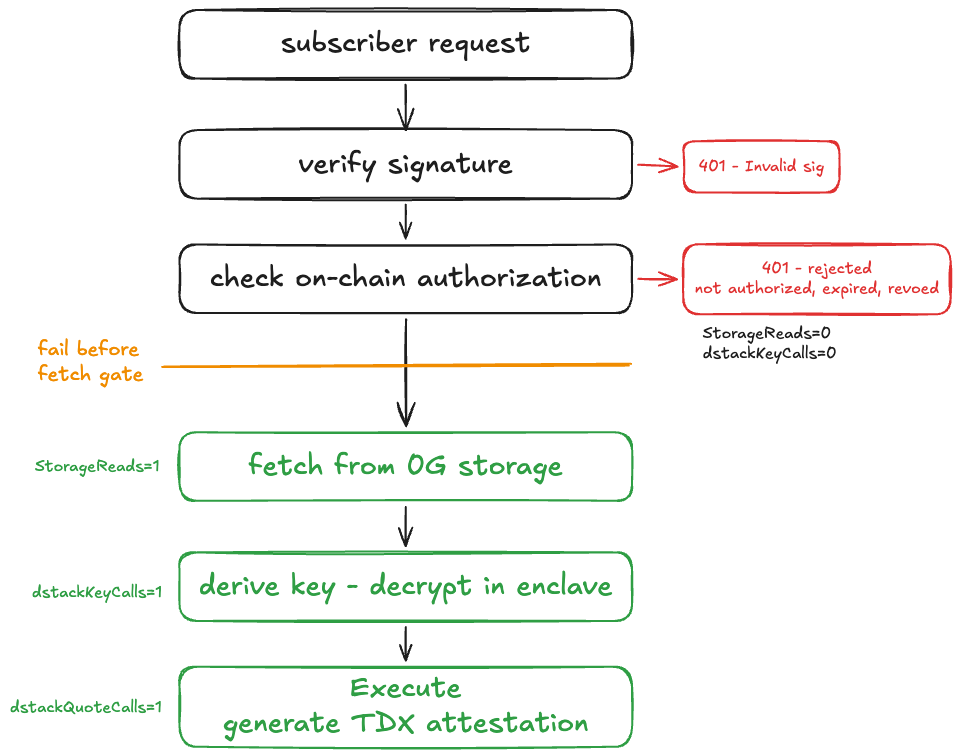
5. When a subscriber invokes the executor, it checks authorization before touching storage
Fail-before-fetch
Unauthorized, expired, and revoked requests produce:
- Storage reads: 0
- Decryption key calls: 0
- No attestation
Only the authorized path proceeds:
- Decrypt inside the enclave
- Execute
- Generate a TDX attestation quote bound to the canonical execution transcript
This prevents replay across different execution contexts.
Validation
Stage 1b-live was validated on 0G mainnet with a Phala Cloud Intel TDX CVM.
The TDX quote was independently verified by proof.t16z.com as a genuine TDX attestation from Intel hardware.
Built on the 0G Stack
- 0G Chain → authorization state and INFT contracts
- 0G Storage → encrypted agent payloads
- ERC-7857 → INFT standard
本次黑客松进展
Phase 1 — Discovery and protocol design
- Confirmed executeSecure() is absent from all 0G Foundation repos despite appearing in official docs. ERC-7857 explicitly acknowledges this as a gap.
- Validated Dstack networking, KMS key derivation, and 0G Storage access from inside Intel TDX CVMs before writing any code.
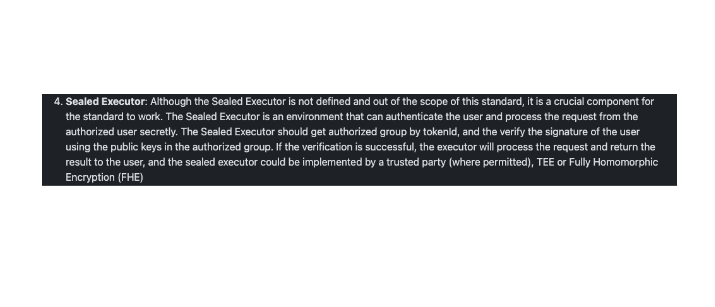
- Designed the protocol with three trust assumptions: Intel TDX hardware, Phala Cloud KMS, and 0G Chain for authorization state.
Phase 2 — Stage 1a: Authorization logic validated
- Deployed INFT.sol and SealedExecutorRegistry.sol to 0G Galileo testnet, both verified on ChainScan.
- Built TypeScript Sealed Executor runtime: signature check, on-chain authorization gate, AES-256-GCM decryption, 0G Storage integration, and fail-before-fetch enforcement.
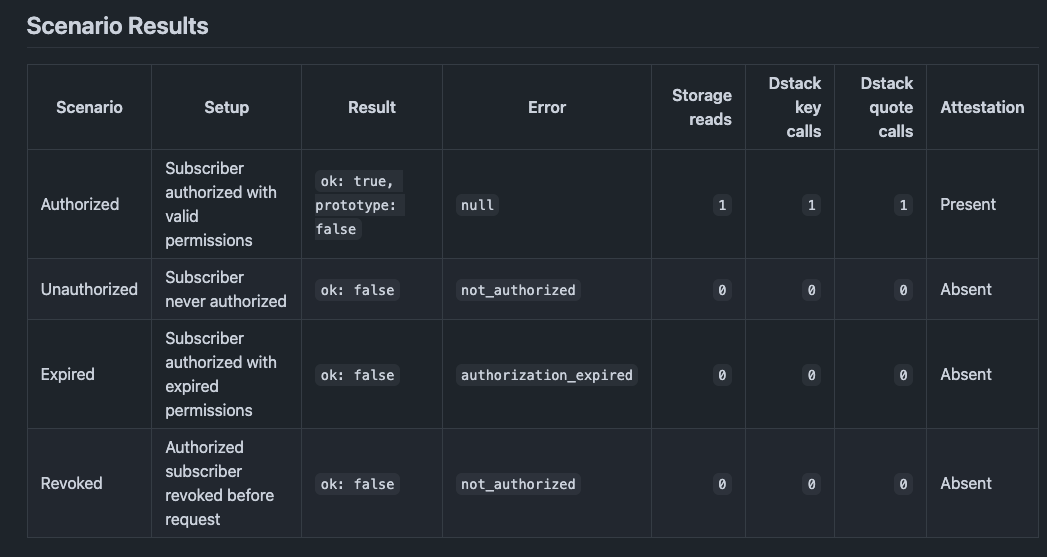
- Validated four scenarios against live testnet.
Phase 3 — Stage 1b: Intel TDX integration
- Integrated Dstack SDK: KMS key derivation and TDX attestation quote generation, replacing the hardcoded development key.
- Implemented AttestationTranscript canonical binding: reportData = sha256(transcript), preventing replay across execution contexts.
- Added quoteReportData verification fail-closed and simulator-in-production guard.
- 40 unit tests passing, 4 integration scenarios passing with simulator.
Phase 4 — Stage 1b-live: Real Intel TDX on Phala Cloud
- Deployed to Phala Cloud CVM (Intel TDX, dstack-dev-0.5.9) using production docker-compose with no simulator environment.
- Built one-shot capture script running entirely inside the CVM: derive live KMS key, encrypt and upload to 0G Storage, mint INFT, run all four scenarios, generate TDX attestation quote.
Measured security invariant, all three rejected paths produced:
storageReads = 0 · dstackKeyCalls = 0 · no attestation quote
TDX quote independently verified by proof.t16z.com. MRCONFIG in the verified quote contains the docker-compose hash, confirming the deployed code matches the committed source.
Phase 5 — Mainnet proof deployment
- Deployed INFT and SealedExecutorRegistry to 0G mainnet (chain ID 16661), both verified on chainscan.0g.ai.
- Ran full Stage 1b-live capture against mainnet contracts with a new Phala Cloud CVM.
- All four authorization scenarios passed. Mainnet TDX attestation quote independently verified. Full evidence package committed to the repository.
融资状态
Not currently fundraising